Two Player's Quantum Covert Lottery
日本語版: https://zenn.dev/yyu/articles/79c6c48226166aa0e875
Introduction
The word “covert lottery” is a security protocol introduced by Card-Based Covert Lottery[1]. In this protocol, there are two players and they input each secret request then:
- If these two requests are not the same, the protocol approve their requests
- Otherwise the requests are the same, the protocol decides either one player's request at random
For example, in Chess game we can use covert lottery to determine if the players take the first move or the second move. These players have their requests but since one's request would be known by the other player, the strategy maybe leak. Covert lottery protocol outputs the actual their requests as long as the requests are not the same, and otherwise it outputs a random result. Both players cannot know if the output reflects their requests or random so there is no information leak.
In the original paper, the protocol is implemented using card-based cryptography[2].I read it and I think it also can be done using quantum technics. So I'll show that the quantum version of covert lottery protocol in this article.
Discussions and questions are very welcome! If you have something you want to ask, please let me know about it.
Two Players Covert Lottery Function
At first I explain about covert lottery in the original paper. There are two players: whose name are Alice and Bob. Alice input is
Note that NOT operation for
Considering
In case of
Quantum Covert Lottery based on BB84
I show that the naive protocol using quantum computer at first.
Protocol
-
Alice generates 1 bit random
x \xleftarrow{\text{rnd}} \{0, 1\} a \in \{0, 1\} -
Alice decides 1 qubit
\ket{\psi_{a,x}} a, x \def\bra#1{\mathinner{\left\langle{#1}\right|}} \def\ket#1{\mathinner{\left|{#1}\right\rangle}} \left\{ \begin{array}{lcl} \ket{\psi_{0,0}} & \equiv & \ket{0} \\ \ket{\psi_{0,1}} & \equiv & \ket{1} \\ \ket{\psi_{1,0}} & \equiv & \ket{+} \\ \ket{\psi_{1,1}} & \equiv & \ket{-} \end{array} \right. - where
\ket{\pm} \equiv \frac{1}{\sqrt{2}}\left(\ket{0} \pm \ket{1}\right)
- where
-
Alice sends
\ket{\psi_{a,x}} -
Bob receives
\ket{\psi_{a,x}} b \in \{0, 1\} -
Bob select the ground state
\mathcal{B}_{\overline{b}} \ket{\psi_{a,x}} y \mathcal{B}_{\overline{b}} \equiv \left\{\ket{\psi_{\overline{b},0}}, \ket{\psi_{\overline{b},1}}\right\} - Note that it requires
\overline{b} b
- Note that it requires
-
Bob sends
y -
Alice receives
y a \oplus x \oplus y
Description
The following table shows that
|
|
|
|||||
|
|
|
|||||
|
|
|
|||||
|
|
|
|||||
|
|
|
|||||
|
|
|
|||||
|
|
|
|||||
|
|
|
The result
- Assuming that
a = \overline{b}\,(\Rightarrow a \ne b) y x - On the other hand,
y a \ne \overline{b} a \oplus x \oplus y
- On the other hand,
- If
a = \overline{b} x = y x a \oplus x \oplus y y a
Security Assumption
The final result of this protocol is calculated by Alice. If Alice is not honest she can change the result into what she wants. So the protocol works well under assuming that at least Alice is semi-honest.
Bob's request leakage
This naive protocol has a vulnerability that Alice can know the Bob's request in some cases. For example:
- Alice select
a = 0, x = 0 \ket{0} - Bob choose
\overline{b} = 1\,(\Rightarrow b = 0) - In the case, he measures using
\ket{0} \left\{\ket{+}, \ket{-}\right\} y 0 1 - If
y = 0
- If
- But if
y = 1 \overline{b} = 1 y = 0 \left\{\ket{0}, \ket{1}\right\}
The protocol result is valid as
CZ Gate and 1 Qubit Measurement-Based Quantum Computation
In this section, I introduce
CZ Gate
- If the first qubit is
\ket{0} CZ - Otherwise
CZ Z
For example,
Note that: the
1 Qubit Measurement-Based Quantum Computation
Considering the measurement of
And
Finally using Hadamard gate
If the result of the measurement is
Definitions of Hadamard gate
Two Player's “Blind” Quantum Covert Lottery
This section is more complicated.
Protocol
-
Alice choose a random angle
\theta \xleftarrow{\text{rnd}} \left\{0, \frac{1\pi}{4}, \dots, \frac{7\pi}{4}\right\} -
Alice sends the following 1 qubit
\ket{+_\theta} \ket{+_\theta} \equiv \frac{1}{\sqrt{2}}\left(\ket{0} + e^{-i\theta}\ket{1}\right) -
Bob apply
CZ \ket{+_\theta} \ket{+} CZ\ket{+_\theta}_1\ket{+}_2 -
CZ\ket{+_\theta}_1\ket{+}_2 CZ\ket{+_\theta}_1\ket{+}_2 = \frac{1}{\sqrt{2}}\ket{0}_1\ket{+}_2 + \frac{e^{-i\theta}}{\sqrt{2}}\ket{1}_1\ket{-}_2
-
-
Alice choose her request
a \in {0, 1} x \xleftarrow{\text{rnd}} \{0, 1\} \delta \delta := \left\{ \begin{array}{ll} \theta + x\pi& \text{if}\; a = 0 \\ \theta + \frac{\pi}{2} + x\pi & \text{if}\; a = 1 \end{array} \right. -
Bob prepares ground state
\left\{\ket{0} \pm e^{i\delta}\ket{1}\right\} \delta y -
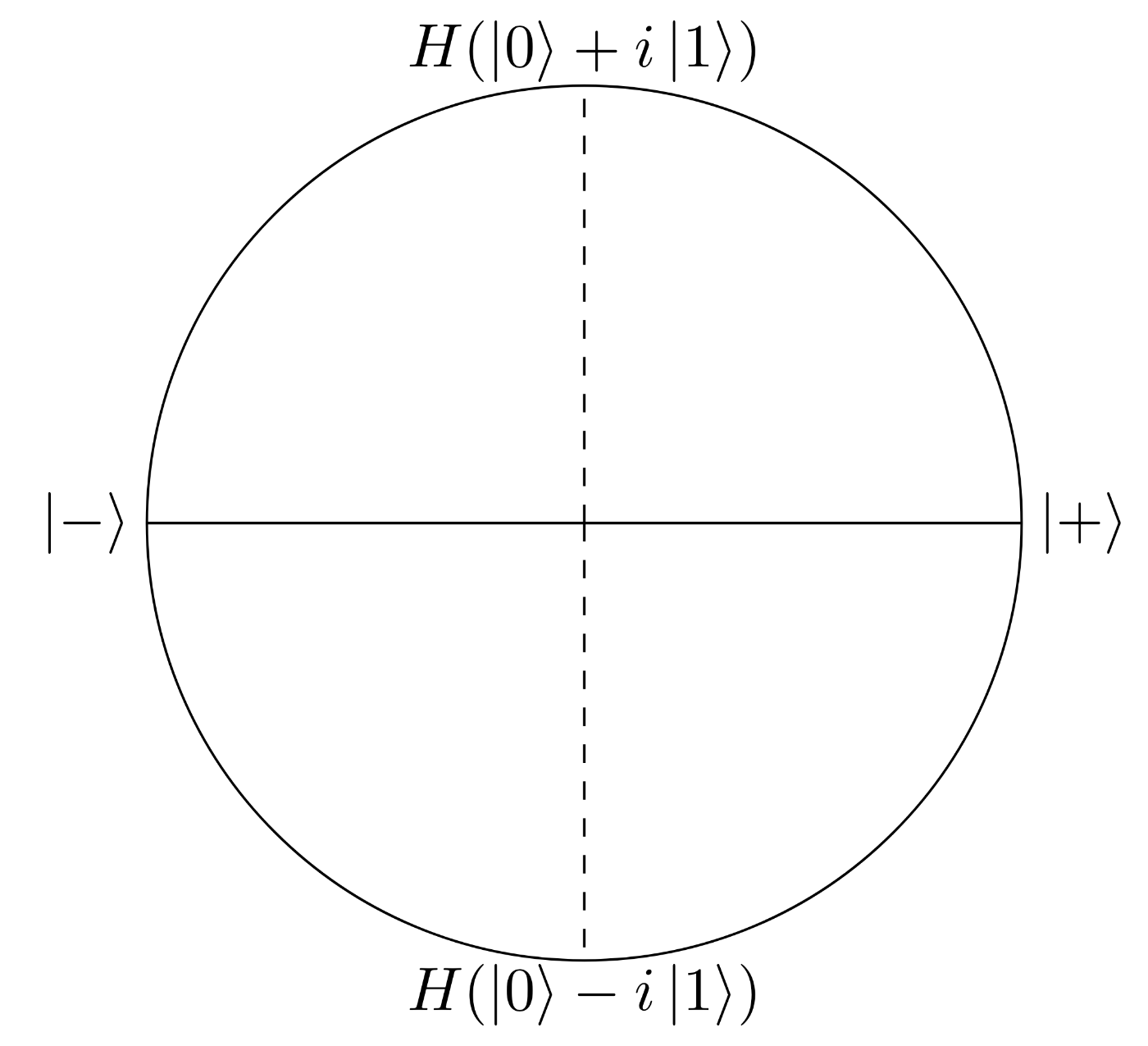
Bob choose his request
b \in \{0, 1\} \mathcal{B}_{\overline{b}} b \left\{ \begin{array}{lcl} \mathcal{B}_{0} & \equiv & \left\{\ket{\pm}\right\} \\ \mathcal{B}_{1} & \equiv & \left\{\frac{1}{\sqrt{2}}\left(\ket{0} \pm i\ket{1}\right)\right\} \end{array} \right. -
Bob measures the second qubit using
\mathcal{B}_{\overline{b}} z z -
Alice outputs
a \oplus x \oplus z
Protocol Behavior
It's difficult to understand the procedure (5). The second qubit is as follows after Bob measured the first qubit using
-
In case
y = 0 \begin{align*} HR_Z(\delta)\ket{+_\theta} &= H\left(\ket{0} + e^{-i\theta}\cdot e^{i\delta}\ket{1}\right) \\ &= H\left(\ket{0} + e^{i(\delta - \theta)}\ket{1}\right) \end{align*} -
In case
y = 1 XHR_Z(\delta)\ket{+_\theta} = XH\left(\ket{0} + e^{i(\delta - \theta)}\ket{1}\right)
This means that what the second qubit would be depends on
| Second qubit | ||||
|---|---|---|---|---|
If
-
Bob's ground state is
\{\ket{\pm}\} \ket{\pm}\bra{\pm}\left(\frac{1}{\sqrt{2}}(i\ket{0} + \ket{1})\right) = \left(\frac{1}{2}i \pm \frac{1}{2}\right)\ket{\pm} - The probability that the result would be
\ket{\pm} \left|\frac{1}{2}i \pm \frac{1}{2}\right|^2 = \sqrt{\left(\frac{1}{2}\right)^2 + \left(\frac{\pm 1}{2}\right)^2}^2 = \frac{1}{2}
- The probability that the result would be
-
Bob's ground state is
\{\frac{1}{\sqrt{2}}\left(\ket{0} \pm i\ket{1}\right)\} \left(\frac{1}{\sqrt{2}}\left(\ket{0} \pm i\ket{1}\right)\right)\left(\frac{1}{\sqrt{2}}\left(\bra{0} \pm i\bra{1}\right)\right)\left(\frac{1}{\sqrt{2}}(i\ket{0} + \ket{1})\right)\\ \,\\ = \left\{ \begin{array}{ll} \left(\frac{1}{2}i + \frac{1}{2}i = i\right)\frac{1}{\sqrt{2}}\left(\ket{0} + i\ket{1}\right) & \text{if}\; \frac{1}{\sqrt{2}}\left(\ket{0} + i\ket{1}\right) \\ \\ \left(\frac{1}{2}i - \frac{1}{2}i = 0\right)\frac{1}{\sqrt{2}}\left(\ket{0} - i\ket{1}\right) & \text{if}\; \frac{1}{\sqrt{2}}\left(\ket{0} - i\ket{1}\right) \end{array} \right. - So the probability that the result would be
\frac{1}{\sqrt{2}}\left(\ket{0} + i\ket{1}\right) |i|^2 = 1 |0|^2 = 0
- So the probability that the result would be
In case Alice's request
In procedure (6) Bob choose
Finally the result of this protocol is
Random value x
In procedure (4), you maybe doubted whether a random value
| Second qubit | |||
|---|---|---|---|
The second qubit is either one of the red parts of the following figure.
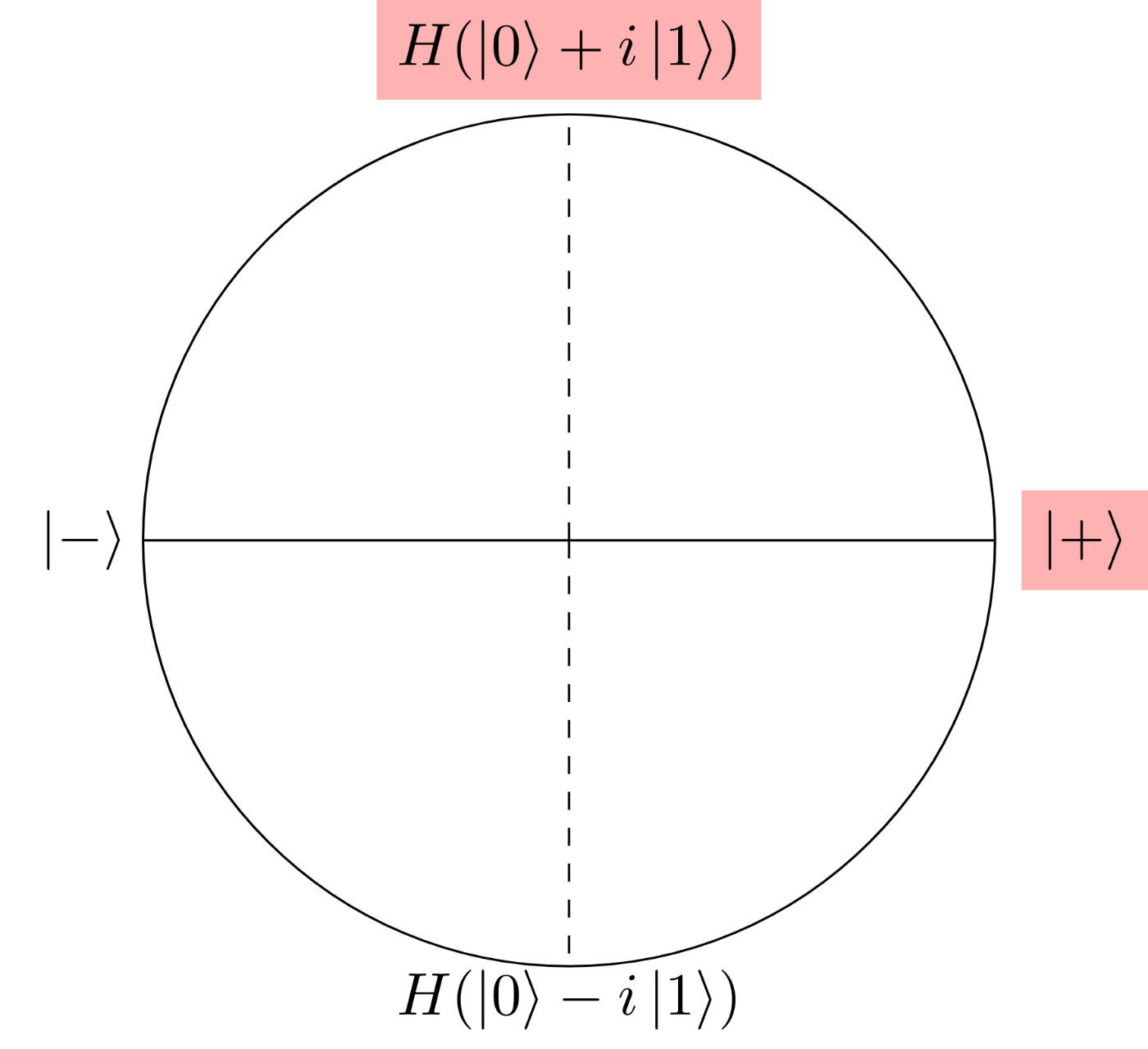
Similar to the naive protocol, if the result would be
Conclusion
I explained two quantum covert lottery protocols. In the original paper, the author extends two-party protocol to many-party. So I want to extend this quantum version protocol to many-party.
References
- 量子コンピュータで2人の“Covert”⁉️ガチャ (Japanese)
- Card-Based Covert Lottery
- 観測に基づく量子計算 (Japanese)
- 量子計算理論 量子コンピュータの原理 (Japanese)
- 量子コンピューティング: 基本アルゴリズムから量子機械学習まで (Japanese)
Discussion