Istio | Getting Started
0. Prerequisite
- A local Kubernetes cluster must be running.
- The version of Istio is
1.15.0.
FYI:
1. Download and Install Istio CLI
Before you can get started configuring Istio, you will need to install the command line tools.
% curl -L https://istio.io/downloadIstio | sh -
...
...
Istio 1.15.0 Download Complete!
Istio has been successfully downloaded into the istio-1.15.0 folder on your system.
...
...
Need more information? Visit https://istio.io/latest/docs/setup/install/
%
% ls | grep istio-1.15.0
istio-1.15.0
%
% echo 'export ISTIO_VERSION="1.15.0"' >> ${HOME}/.zshrc
% source ${HOME}/.zshrc
% echo $ISTIO_VERSION
1.15.0
%
% cd istio-1.15.0
% ls
LICENSE bin manifests tools
README.md manifest.yaml samples
% sudo cp -v bin/istioctl /usr/local/bin/
Password:
bin/istioctl -> /usr/local/bin/istioctl
%
% which istioctl
/usr/local/bin/istioctl
%
% istioctl version
no running Istio pods in "istio-system"
1.15.0
%
2. Install all the Istio components
Install all the Istio components using the built-in demo configuration profile.
This installation lets you quickly get started evaluating Istio.
% istioctl install --set profile=demo -y
✔ Istio core installed
✔ Istiod installed
✔ Ingress gateways installed
✔ Egress gateways installed
✔ Installation complete Making this installation the default for injection and validation.
Thank you for installing Istio 1.15. Please take a few minutes to tell us about your install/upgrade experience! https://forms.gle/SWHFBmwJspusK1hv6
%
% kubectl -n istio-system get svc
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
istio-egressgateway ClusterIP 10.105.101.50 <none> 80/TCP,443/TCP 5m29s
istio-ingressgateway LoadBalancer 10.108.35.166 <pending> 15021:31061/TCP,80:31614/TCP,443:30228/TCP,31400:32341/TCP,15443:30312/TCP 5m29s
istiod ClusterIP 10.100.247.44 <none> 15010/TCP,15012/TCP,443/TCP,15014/TCP 5m53s
%
% kubectl -n istio-system get pods
NAME READY STATUS RESTARTS AGE
istio-egressgateway-564bdb69c7-l9cn7 1/1 Running 0 5m38s
istio-ingressgateway-984565b57-n5vtm 1/1 Running 0 5m38s
istiod-6b5cbd4c58-vh44h 1/1 Running 0 6m2s
%
3. Automatically inject Envoy sidecar proxies
Install the Bookinfo application inside its own namespace(bookinfo) and allow Istio to automatically inject the Sidecar Proxy.
% kubectl create namespace bookinfo
namespace/bookinfo created
% kubectl get namespace
NAME STATUS AGE
bookinfo Active 11s
default Active 80m
istio-system Active 14m
kube-node-lease Active 80m
kube-public Active 80m
kube-system Active 80m
%
% kubectl get ns bookinfo --show-labels
NAME STATUS AGE LABELS
bookinfo Active 4m6s kubernetes.io/metadata.name=bookinfo
%
% kubectl label namespace bookinfo istio-injection=enabled
namespace/bookinfo labeled
%
% kubectl get ns bookinfo --show-labels
NAME STATUS AGE LABELS
bookinfo Active 4m44s istio-injection=enabled,kubernetes.io/metadata.name=bookinfo
%
4. Deploy the sample application
Deploy the Bookinfo sample application.
% cd istio-1.15.0
% kubectl -n bookinfo apply -f samples/bookinfo/platform/kube/bookinfo.yaml
service/details created
serviceaccount/bookinfo-details created
deployment.apps/details-v1 created
service/ratings created
serviceaccount/bookinfo-ratings created
deployment.apps/ratings-v1 created
service/reviews created
serviceaccount/bookinfo-reviews created
deployment.apps/reviews-v1 created
deployment.apps/reviews-v2 created
deployment.apps/reviews-v3 created
service/productpage created
serviceaccount/bookinfo-productpage created
deployment.apps/productpage-v1 created
%
% kubectl -n bookinfo get pod,svc
NAME READY STATUS RESTARTS AGE
pod/details-v1-76778d6644-mddfc 2/2 Running 0 3m37s
pod/productpage-v1-7c548b785b-zwxdt 2/2 Running 0 3m37s
pod/ratings-v1-85c74b6cb4-k8qcp 2/2 Running 0 3m37s
pod/reviews-v1-6494d87c7b-jdzg2 2/2 Running 0 3m37s
pod/reviews-v2-79857b95b-69nfq 2/2 Running 0 3m37s
pod/reviews-v3-75f494fccb-9xxzb 2/2 Running 0 3m37s
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
service/details ClusterIP 10.96.190.145 <none> 9080/TCP 3m37s
service/productpage ClusterIP 10.97.154.226 <none> 9080/TCP 3m37s
service/ratings ClusterIP 10.107.207.179 <none> 9080/TCP 3m37s
service/reviews ClusterIP 10.99.133.26 <none> 9080/TCP 3m37s
%
% kubectl -n bookinfo get pod -l app=ratings
NAME READY STATUS RESTARTS AGE
ratings-v1-85c74b6cb4-k8qcp 2/2 Running 0 9m6s
%
% kubectl -n bookinfo exec -it ratings-v1-85c74b6cb4-k8qcp -- /bin/bash
node@ratings-v1-85c74b6cb4-k8qcp:/opt/microservices$ ls -la
total 36
drwxr-xr-x 1 root root 4096 May 18 20:50 .
drwxr-xr-x 1 root root 4096 May 18 20:50 ..
drwxr-xr-x 25 root root 4096 May 18 20:50 node_modules
-rw-r--r-- 1 root root 7350 May 18 20:50 package-lock.json
-rw-r--r-- 1 root root 158 May 10 13:42 package.json
-rw-r--r-- 1 root root 8864 May 10 13:42 ratings.js
node@ratings-v1-85c74b6cb4-k8qcp:/opt/microservices$ whoami
node
node@ratings-v1-85c74b6cb4-k8qcp:/opt/microservices$ curl -sS http://productpage:9080/productpage | grep -o "<title>.*</title>"
<title>Simple Bookstore App</title>
node@ratings-v1-85c74b6cb4-k8qcp:/opt/microservices$ exit
exit
%
5. Open the application to outside traffic
The Bookinfo application is deployed but not accessible from the outside.
To make it accessible, you need to create an Istio Ingress Gateway.
5.1. Create an Istio Ingress Gateway
Associate this application with the Istio gateway.
Ensure that there are no issues with the configuration.
% cd istio-1.15.0
% kubectl -n bookinfo apply -f samples/bookinfo/networking/bookinfo-gateway.yaml
gateway.networking.istio.io/bookinfo-gateway created
virtualservice.networking.istio.io/bookinfo created
%
% istioctl -n bookinfo analyze
✔ No validation issues found when analyzing namespace: bookinfo.
%
5.2. Determining the ingress IP and ports
Run minikube tunnel command in a new terminal window to start a Minikube tunnel that sends traffic to your Istio Ingress Gateway.
This will provide an external load balancer, EXTERNAL-IP, for service/istio-ingressgateway.
% minikube tunnel
✅ Tunnel successfully started
📌 NOTE: Please do not close this terminal as this process must stay alive for the tunnel to be accessible ...
...
...
% kubectl -n istio-system get service istio-ingressgateway
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
istio-ingressgateway LoadBalancer 10.108.35.166 127.0.0.1 15021:31061/TCP,80:31614/TCP,443:30228/TCP,31400:32341/TCP,15443:30312/TCP 55m
%
% export INGRESS_HOST=$(kubectl -n istio-system get service istio-ingressgateway -o jsonpath='{.status.loadBalancer.ingress[0].ip}')
% export INGRESS_PORT=$(kubectl -n istio-system get service istio-ingressgateway -o jsonpath='{.spec.ports[?(@.name=="http2")].port}')
% export SECURE_INGRESS_PORT=$(kubectl -n istio-system get service istio-ingressgateway -o jsonpath='{.spec.ports[?(@.name=="https")].port}')
% echo "$INGRESS_HOST"
127.0.0.1
% echo "$INGRESS_PORT"
80
% echo "$SECURE_INGRESS_PORT"
443
%
% export GATEWAY_URL=$INGRESS_HOST:$INGRESS_PORT
% echo "$GATEWAY_URL"
127.0.0.1:80
%
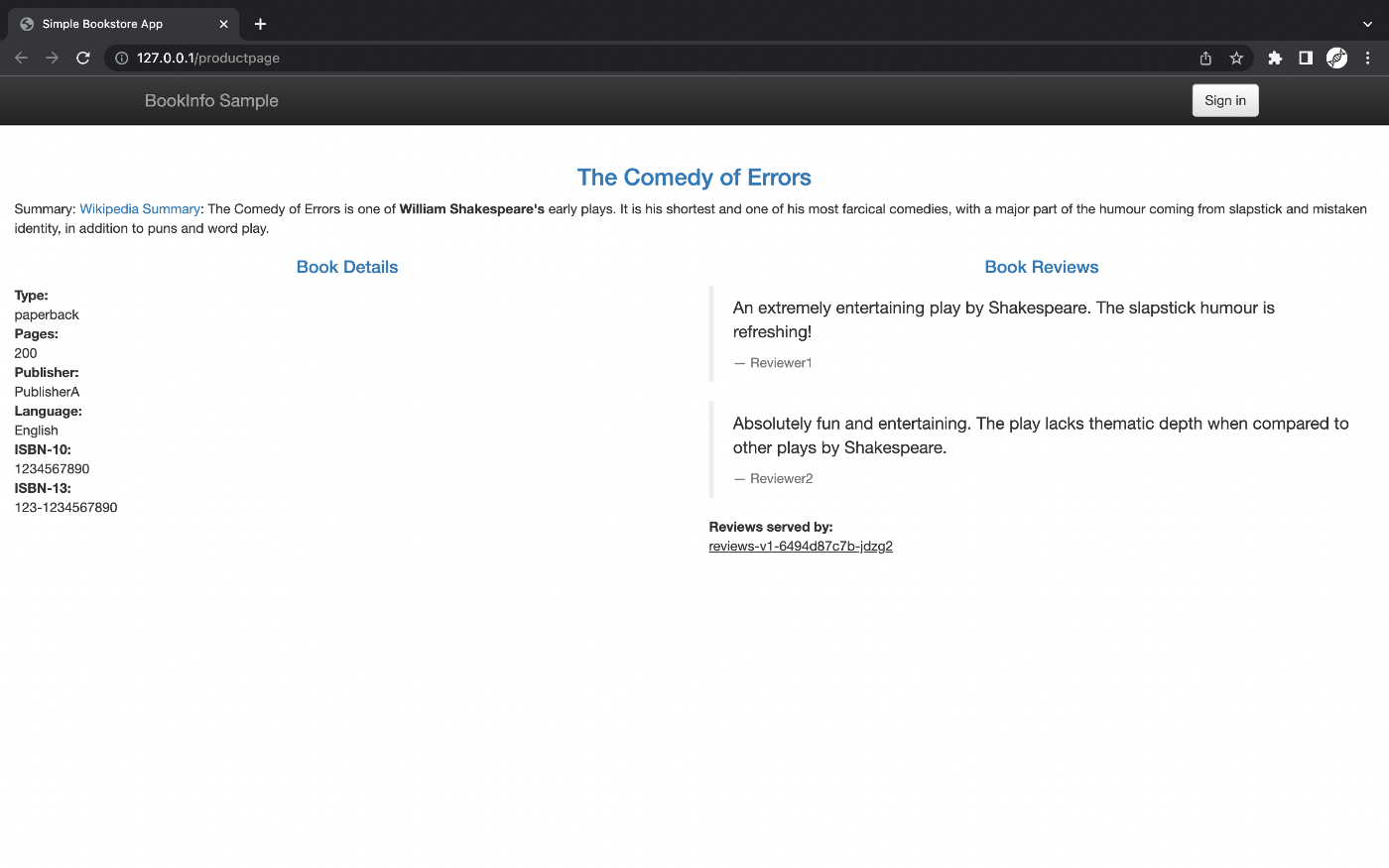
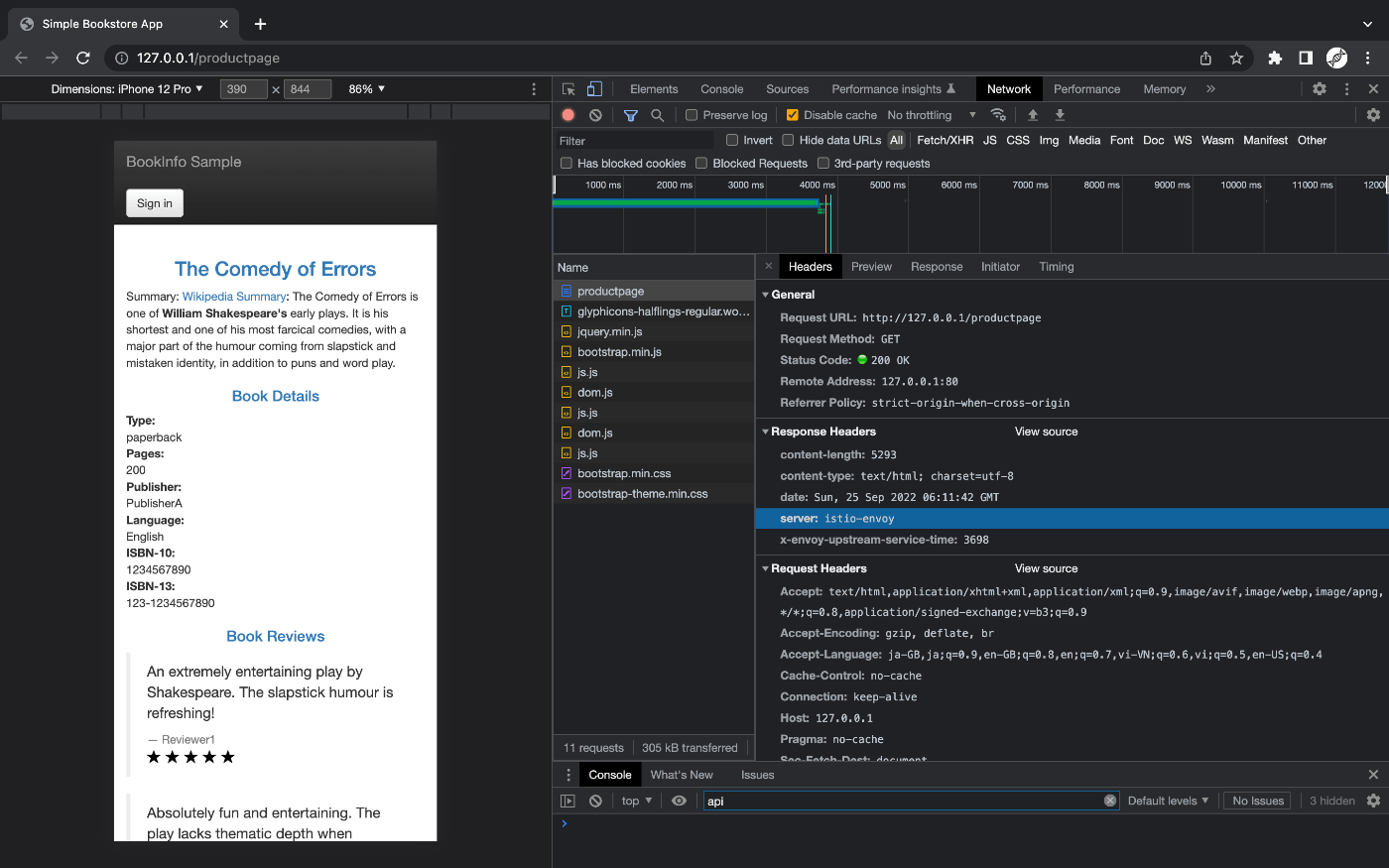
5.3. Verify external access
Confirm that the Bookinfo application is accessible from outside by viewing the Bookinfo product page using a browser.
% echo "http://$GATEWAY_URL/productpage"
http://127.0.0.1:80/productpage
%
% curl -sS http://127.0.0.1:80/productpage | grep -o "<title>.*</title>"
<title>Simple Bookstore App</title>
%
Screenshot
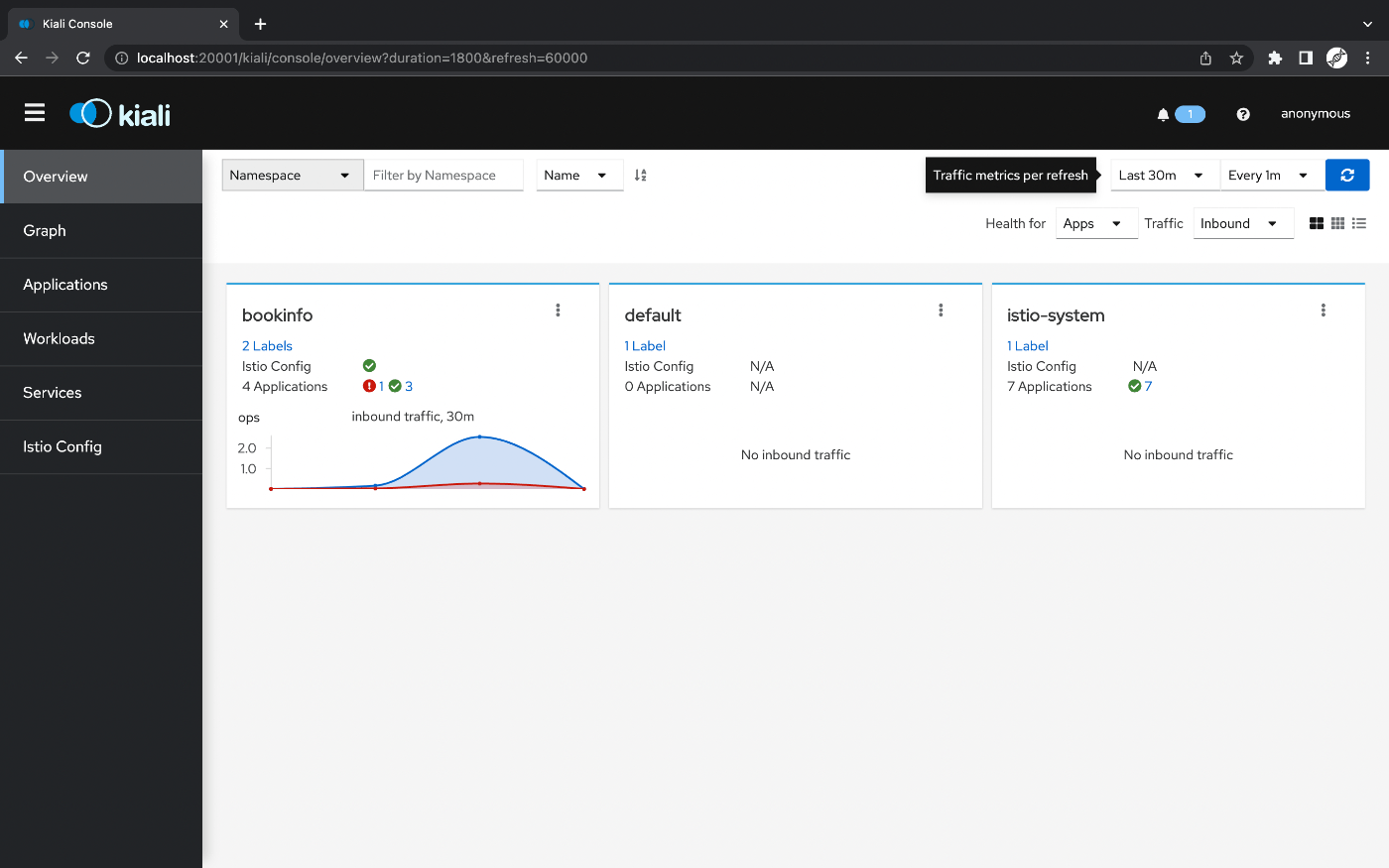
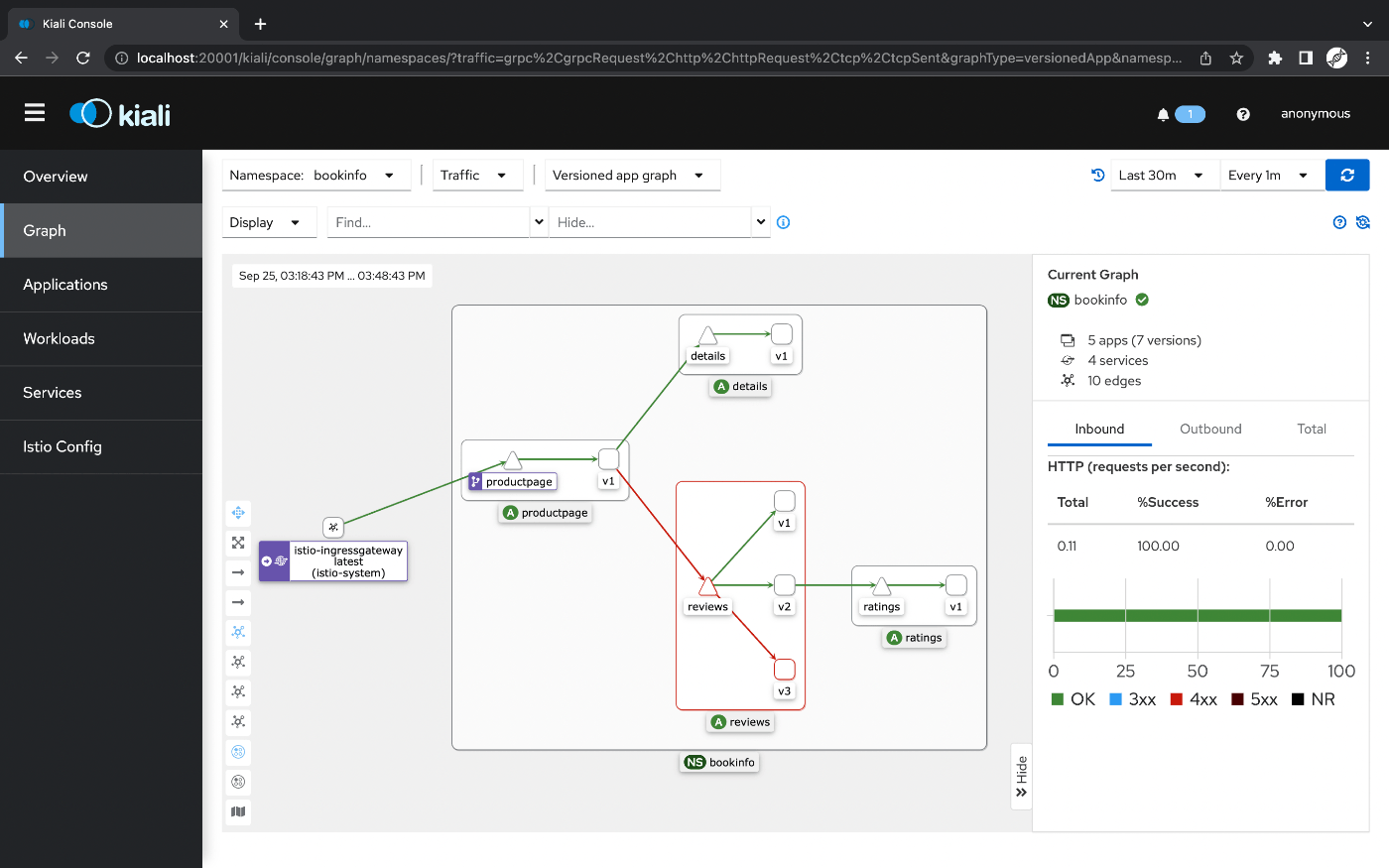
6. View the Kiali dashboard
Istio integrates with several different telemetry applications.
These can help you gain an understanding of the structure of your service mesh, display the topology of the mesh, and analyze the health of your mesh.
Use the following instructions to deploy the Kiali dashboard, along with Prometheus, Grafana, and Jaeger.
% cd istio-1.15.0
% kubectl -n istio-system apply -f samples/addons
serviceaccount/grafana created
configmap/grafana created
service/grafana created
deployment.apps/grafana created
configmap/istio-grafana-dashboards created
configmap/istio-services-grafana-dashboards created
deployment.apps/jaeger created
service/tracing created
service/zipkin created
service/jaeger-collector created
serviceaccount/kiali created
configmap/kiali created
clusterrole.rbac.authorization.k8s.io/kiali-viewer created
clusterrole.rbac.authorization.k8s.io/kiali created
clusterrolebinding.rbac.authorization.k8s.io/kiali created
role.rbac.authorization.k8s.io/kiali-controlplane created
rolebinding.rbac.authorization.k8s.io/kiali-controlplane created
service/kiali created
deployment.apps/kiali created
serviceaccount/prometheus created
configmap/prometheus created
clusterrole.rbac.authorization.k8s.io/prometheus created
clusterrolebinding.rbac.authorization.k8s.io/prometheus created
service/prometheus created
deployment.apps/prometheus created
%
% kubectl -n istio-system get deploy
NAME READY UP-TO-DATE AVAILABLE AGE
grafana 1/1 1 1 105s
istio-egressgateway 1/1 1 1 85m
istio-ingressgateway 1/1 1 1 85m
istiod 1/1 1 1 85m
jaeger 1/1 1 1 105s
kiali 1/1 1 1 104s
prometheus 1/1 1 1 104s
%
% kubectl rollout status deployment/kiali -n istio-system
deployment "kiali" successfully rolled out
%
% for i in $(seq 1 100); do curl -s -o /dev/null "http://$GATEWAY_URL/productpage"; done
%
% istioctl dashboard kiali
http://localhost:20001/kiali
...
...
Screenshot
Discussion